IT Security Policy for Startups: A Step-by-Step Implementation Guide
Startups are moving faster than ever — building products, scaling teams, and acquiring users at an incredible pace. But in the rush to grow, one critical area often gets overlooked: IT security.
In 2025, startups are one of the most common targets for cyberattacks. Why? Because attackers know that early-stage companies typically lack structured security systems, formal policies, and dedicated security teams.
A single security breach can lead to data loss, legal penalties, customer churn, and irreversible damage to your brand. For startups trying to build trust and secure enterprise clients, this can be devastating.
This is why having a well-defined IT security policy is no longer optional — it is a foundational requirement.
This guide walks you through how to build a complete, practical, and scalable IT security policy for your startup.
What Is an IT Security Policy?
An IT security policy is a formal document that defines how your organization protects its digital assets, systems, and data from unauthorized access, breaches, and cyber threats.
It establishes rules, procedures, and responsibilities for maintaining security across your organization.
A strong IT security policy helps:
- Protect sensitive data
- Ensure regulatory compliance
- Build trust with customers and partners
- Reduce the risk of cyber incidents
For startups, it also plays a critical role in enterprise sales, where security requirements are often mandatory.
Legal and Compliance Requirements
Even if your startup is small, you are still expected to follow certain security standards depending on your market and customers.
GDPR (Article 32)
Requires organizations to implement appropriate technical and organizational measures to protect personal data.
ISO 27001
A globally recognized standard for information security management systems.
SOC 2
Commonly required for SaaS startups, focusing on security, availability, and confidentiality.
These frameworks emphasize risk management, data protection, and accountability.
The 12 Core Components of an IT Security Policy
A complete IT security policy should include the following components:
- Access control policy
- Password and authentication policy
- Device and endpoint security
- Remote access policy
- Data classification and handling
- Incident response plan
- Backup and recovery policy
- Vendor and third-party security
- Network security guidelines
- Employee training and awareness
- Monitoring and logging
- Compliance and audit procedures
Each component contributes to building a secure and resilient system.
Access Control and Privilege Management
Access control is the foundation of your security system. It ensures that only authorized individuals can access specific resources.
Best Practices
- Use role-based access control (RBAC)
- Grant least privilege access
- Regularly review permissions
- Revoke access immediately when employees leave
Proper access control minimizes the risk of internal threats and accidental data exposure.
Password Policy and Multi-Factor Authentication (MFA)
Weak passwords are one of the most common causes of security breaches.
Strong Password Policy Includes:
- Minimum length requirements
- Combination of characters
- Regular password updates
- Password managers
Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring additional verification beyond passwords.
It is one of the most effective ways to prevent unauthorized access.
Device and BYOD (Bring Your Own Device) Policy
Startups often allow employees to use personal devices for work. While convenient, this increases security risks.
Your BYOD Policy Should Define:
- Approved devices
- Security requirements (encryption, antivirus)
- Remote wipe capabilities
- Access restrictions
This ensures that personal devices do not become weak points in your system.
Remote Access and VPN Policy
With remote work becoming standard, secure access to company systems is critical.
Key Elements
- Use of VPN for secure connections
- Restrictions on public Wi-Fi usage
- Secure authentication methods
- Monitoring remote access activity
Remote access policies protect your systems from external threats.
Data Classification and Handling
Not all data is equal. Your policy should classify data based on sensitivity.
Common Categories
- Public data
- Internal data
- Confidential data
- Restricted data
Each category should have specific handling and storage rules.
This ensures that sensitive data receives the highest level of protection.
Incident Response Plan
No system is completely secure. What matters is how quickly and effectively you respond to incidents.
Key Steps
- Detection and identification
- Containment
- Investigation
- Recovery
- Post-incident review
A well-defined incident response plan minimizes damage and recovery time.
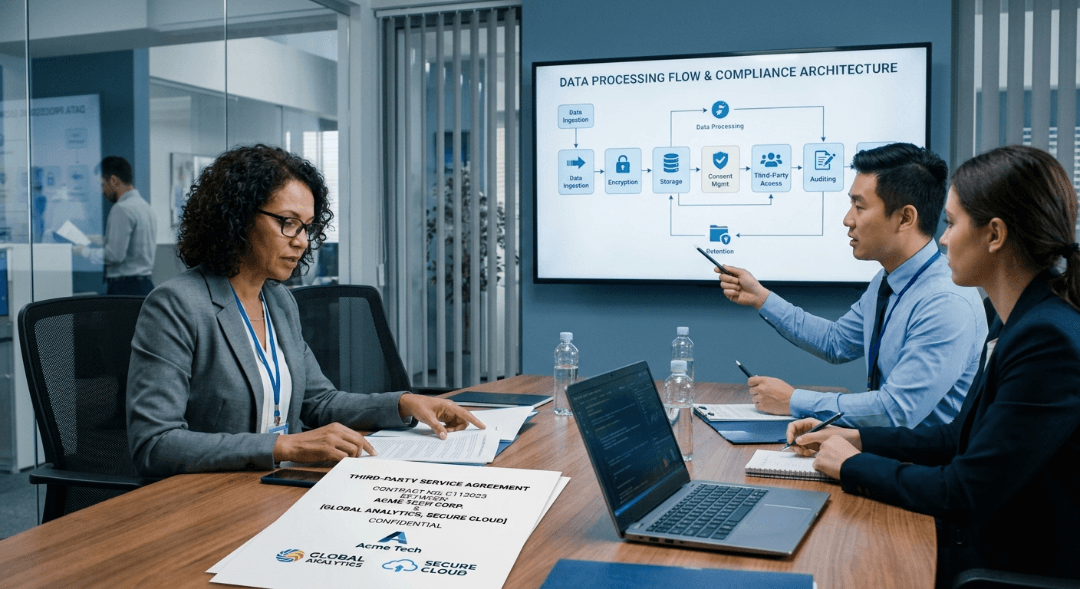
Vendor and Third-Party Security
Most startups rely on third-party tools and services. These vendors can introduce security risks if not properly managed.
Best Practices
- Evaluate vendor security standards
- Use data processing agreements
- Limit data sharing
- Monitor vendor compliance
Your security is only as strong as your weakest vendor.
Employee Security Training
Human error is one of the biggest security risks.
Your policy should include regular training on:
- Phishing awareness
- Password hygiene
- Secure data handling
- Incident reporting
Educated employees are your first line of defense.
IT Security Policy for SaaS vs Hardware Startups
SaaS Startups
Focus heavily on data protection, cloud security, and compliance with frameworks like SOC 2.
Hardware Companies
Need additional focus on physical security, device firmware, and supply chain risks.
Your policy should reflect your business model.
Monitoring and Logging
Continuous monitoring helps detect unusual activity early.
Your policy should define:
- What activities are logged
- How logs are stored
- Who can access logs
This supports both security and compliance.
Backup and Recovery Policy
Data loss can occur due to attacks, system failures, or human error.
Your backup strategy should include:
- Regular automated backups
- Secure storage
- Disaster recovery testing
Reliable backups ensure business continuity.
How Policy Generators Simplify IT Security Policy Creation
Creating a comprehensive IT security policy manually requires significant expertise and time. Policy generators simplify this process by providing structured templates tailored to your business needs.
This allows startups to:
- Quickly establish security frameworks
- Ensure coverage of key components
- Prepare for audits and compliance requirements
It is an efficient way to build a strong security foundation.
Frequently Asked Questions
Do startups really need an IT security policy?
Yes. Even small startups handle sensitive data and are targets for cyberattacks.
How long should an IT security policy be?
It should be detailed enough to cover all critical areas.
Is ISO 27001 required?
Not always required, but often expected for enterprise clients.
How often should policies be updated?
At least annually or after major changes.
Final Thoughts
IT security is no longer just a technical concern — it is a business priority. Startups that invest in strong security policies early are better positioned to scale, win enterprise clients, and build trust.
Instead of reacting to incidents, proactive planning ensures resilience and long-term success.
A strong IT security policy is not just protection — it is a competitive advantage.